Month: July 2019
-

The great web developer con
Another day, another dodgy web developer story. The premise: We would like to offer you a website design for X amount. But to do so, we need to transfer your domain to us. This tale is a pretty old one but it appears to be flourishing – the lure of a good once-off price for…
-
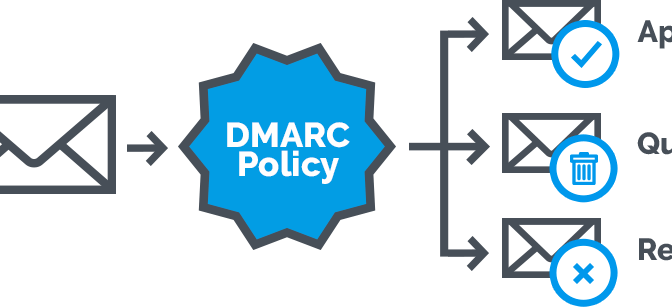
DMARC: optimising email delivery
Email is a fickle thing … There are a huge amount of dependencies involved in what seems like a small task – sending an email. What started out as a simple method of exchanging messages has morphed over the years into a cobbled-together monster as needs changed and especially businesses required a more robust and…
