Tag: email
-

The trouble with SPAM
The queries I’ve been getting lately requesting checks on whether a particular email is spam or not, has been enlightening. It’s clear there’s a problem. Somewhere. Email users are not seeing the “wood for the trees” no matter the fact that spam has been an entrenched part of our lives for a couple of decades…
-
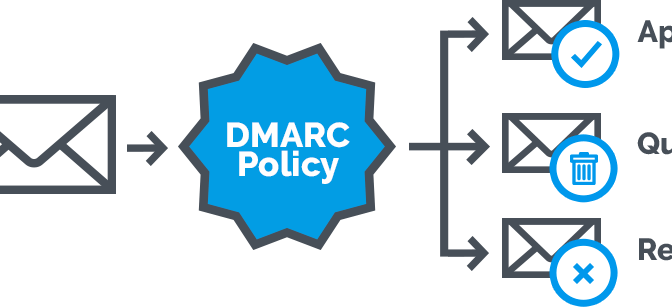
DMARC: optimising email delivery
Email is a fickle thing … There are a huge amount of dependencies involved in what seems like a small task – sending an email. What started out as a simple method of exchanging messages has morphed over the years into a cobbled-together monster as needs changed and especially businesses required a more robust and…
-
A fascination with special characters
In the computer world, special characters can have a certain usefulness or can be a hindrance. The very first special character I learnt 25 years ago, was the colon. It was ( still is ) used as the delimiter to change drive letters in DOS. eg. if you were in drive C and wanted to go…
-
Email delivery ( and some other stuff about email )
Email is still the single most used communications tool on the internet and will probably remain so for some time to come. We send in the region of 300 Billion emails per day and for the most part, everything just works. On the face of it, email is simple: compose, address and send. But behind…
-
New security issue: typo-squatting
Malware, phishing, pharming, typo-squatting, etc. There’s a long list of security issues we have to deal with every day. Keeping track of these and responding correctly in each case is a veritable minefield. That’s after our newly updated anti-virus app has completely missed the threat. Typo-squatting is the well-known practice of serving up scams or…
-
Email woes and etiquette
Based on issues that a client of mine has had in recent times with email, I decided to resurrect and rehash my XStore IT Bulletin no. 1 from July 2006. One of the biggest issues with email is the lack of understanding of how it works. In addition, the requirement to implement anti-spam solutions falls…
-
New email service coming from XStore and SilcomIT
ISPs have recently been getting very strict in terms of email usage on their ADSL networks and have implemented quota management for outbound email when using their smtp relays. As a result, a client could: have email rejected once a certain threshold is reached ( eg. 30 emails per sender per hour ) be disconnected…
