Category: Security
-

The little camera that could
IT and Network Security is a tough arena. Keeping networks, systems and data secure from what can only be called a total onslaught of malware and other malicious attacks, is a difficult task. What makes the task even more difficult is the general indifference of (especially) SMEs to the potential harm that can be caused…
-

Storm in a WhatsApp teacup?
Facebook’s recent update of the Terms of Service for Whatsapp has got a lot of people riled up. And quite rightly so. The core of this issue is not privacy of information as many believe, but rather pure business economics – let’s cover the basics first. There are 2 primary considerations for using cloud services…
-

SSL/TLS Certificate lifetime
The SSL/TLS certificate revocation system (CRL and OCSP) is broken. This is a fact known for a long time by the whole certificate industry. Long-lived certificates that have issues (eg. a certificate that was fraudulently issued), hang around on the Internet for extended periods (currently up to 3 years) potentially causing security and authenticity issues.…
-

Browser Security
Browser technology and security events always make for interesting reading especially due to the fact that we do the majority of our online work these days through browsers, be it general web surfing, accessing enterprise apps or managing systems and devices. Browser features and security are therefore critical – this shouldn’t even need to be…
-

Cloud Services and Availability
From the way that Cloud vendors promote their wares and how apologists fawn over these services, one would think that Cloud was the be all and end all of computing. The fact is that we’ve been here before and Cloud is just a more advanced form of central or mainframe computing from the 60s and…
-

The Apple/Google contact tracing API
Apple and Google (yes generally understood to be “sworn enemies” 😀 ) jointly developed an API to be used by contact tracing apps and released said API late in May 2020. Apple and Google’s API follows a decentralized approach, which means that every operation that might involve privacy is carried out on users’ phones, rather…
-

Are you BIASed?
A new vulnerability in the authentication component of the Bluetooth wireless protocol has been uncovered by a group of researchers. The issue is not relating to a bug but rather the specification itself. “The Bluetooth standard includes both a legacy authentication procedure and a secure authentication procedure, allowing devices to authenticate to each other using…
-

RDP – the gift that keeps on giving
It’s long been known (at least in security circles) that the RDP protocol, as well as client and server implementations, are horribly broken. While a BlueKeep (the most recent RDP vulnerability) worm has yet to surface, brute-force password attacks on RDP services are a dime a dozen and occurring at a rapid rate. PoC code…
-

The great web developer con
Another day, another dodgy web developer story. The premise: We would like to offer you a website design for X amount. But to do so, we need to transfer your domain to us. This tale is a pretty old one but it appears to be flourishing – the lure of a good once-off price for…
-
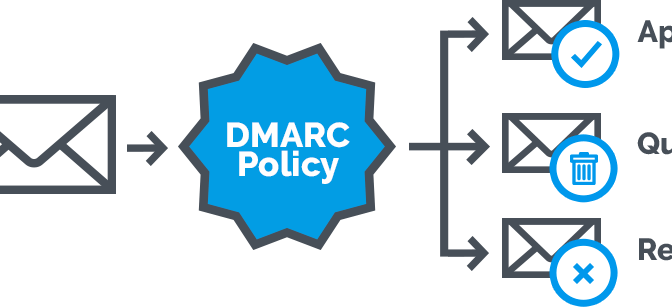
DMARC: optimising email delivery
Email is a fickle thing … There are a huge amount of dependencies involved in what seems like a small task – sending an email. What started out as a simple method of exchanging messages has morphed over the years into a cobbled-together monster as needs changed and especially businesses required a more robust and…
-

Vuln mitigation and INtel MDS – the spectre looms
Spectre and Meltdown a have been with us for just over a year now and even with all the predictions of dire consequences, we have yet to see any in-the-wild code snippets or attacks beyond theoretical POCs. So the question to ask is whether we should be losing a lot of hardware performance (most of…
-

A lesson in supply chain attacks
What happens when the websites we visit and the companies we depend on to provide us with information, are compromised? Supply chain attacks go to the root of information we depend on rather than attack us directly. A recent attack on the Asus infrastructure paints the exact scenario for supply chain attacks. Attackers compromised an…
-
2018 the year of the hacked router
I’ve spoken in depth on consumer (and some enterprise) router security issues. In brief summary, these devices are pieces of scrap that are full of vulnerabilities and very seldom get updated to fix issues. It’s no coincidence that this year has seen an exponential growth in attacks on routers as well as botnets making use…
-
(S)RUM
Veronica Schmitt, a senior digital forensic scientist at DFIRLABS, recently featured on Paul’s Security Weekly, showcasing the Microsoft SRUM system tool (System Resource Utilization Monitor). SRUM was first introduced in Windows 8, and was a new feature designed to track system resource utilization such as CPU cycles, network activity, power consumption, etc. Analysts can use…
-

VPNFilter and other neat tricks
The Spectre and Meltdown attacks that came to light at the beginning of the year have been the main focus of this year’s security issues however there has been a lot more going on than that. On that note though, additional Spectre variations have been found (we’re up to v4 now); as well, the BSD…
